Have I Been Pwned teams up with the FBI to collect a lot more stolen passwords
The FBI now has a direct line to HIBP to inject compromised passwords into its database as it takes down botnets.

Have I Been Pwned, the go-to site for checking if your email or password has been exposed in a data breach (and if so, how many times), has teamed up with the US Federal Bureau of Investigation to bolster its database with compromised credentials in a much more timely fashion. It's also going open source.
The HIBP site is a gem on the internet. It was started by Troy Hunt, a web security consultant and a member of the Microsoft Regional Director program (he's not a Microsoft employee), who was motivated to create the service after a security breach at Adobe in 2013 exposed login credentials for 150 million accounts. It was the largest single-breach of customer accounts at the time.
There are two components to HIBP—one for emails and another for passwords. A record of more than 154 million breached accounts reside in Windows Azure table storage, which users can check separately. While that may sound risky, passwords are not stored next to any personally identifiable information (like emails) and are encrypted via SHA-1 (Secure Hash Algorithm 1).
In a blog post, Hunt explains that the FBI reached out to him about creating a way for the agency to feed compromised passwords directly into HIBP. Hunt says the FBI's goal is "perfectly aligned" with his own, that being to proactively warn people when their accounts have been compromised (users can optionally sign up to receive notifications when a breach tied to their email addresses is detected), and so they are now working together to make it happen. According to Hunt, the FBI will feed compromised passwords into the service nearly 1 billion times every month.
"We are excited to be partnering with HIBP on this important project to protect victims of online credential theft. It is another example of how important public/private partnerships are in the fight against cybercrime," said Bryan A. Vorndran, assistant director of the FBI's cyber division.
The FBI's direct feed into HIBP is still a secure one, with passwords being spooned into the service in SHA-1 and NTLM hash pairs, and not plain text. But what's the upshot here? For users, it means a potentially quicker heads up if and when their accounts have been exposed in a data breach.
"They'll be fed into the system as they're made available by the bureau and obviously that's both a cadence and a volume which will fluctuate depending on the nature of the investigations they're involved in," Hunt says. "The important thing is to ensure there's an ingestion route by which the data can flow into HIBP and be made available to consumers as fast as possible in order to maximize the value it presents."
Keep up to date with the most important stories and the best deals, as picked by the PC Gamer team.
Working together on a direct feed is the next logical step. The FBI recently provided over 4.3 million compromised email addresses to Hunt, that were obtained from taking down the Emotet botnet in January. Creating a direct line means the FBI can do this sort of thing much quicker in the future.
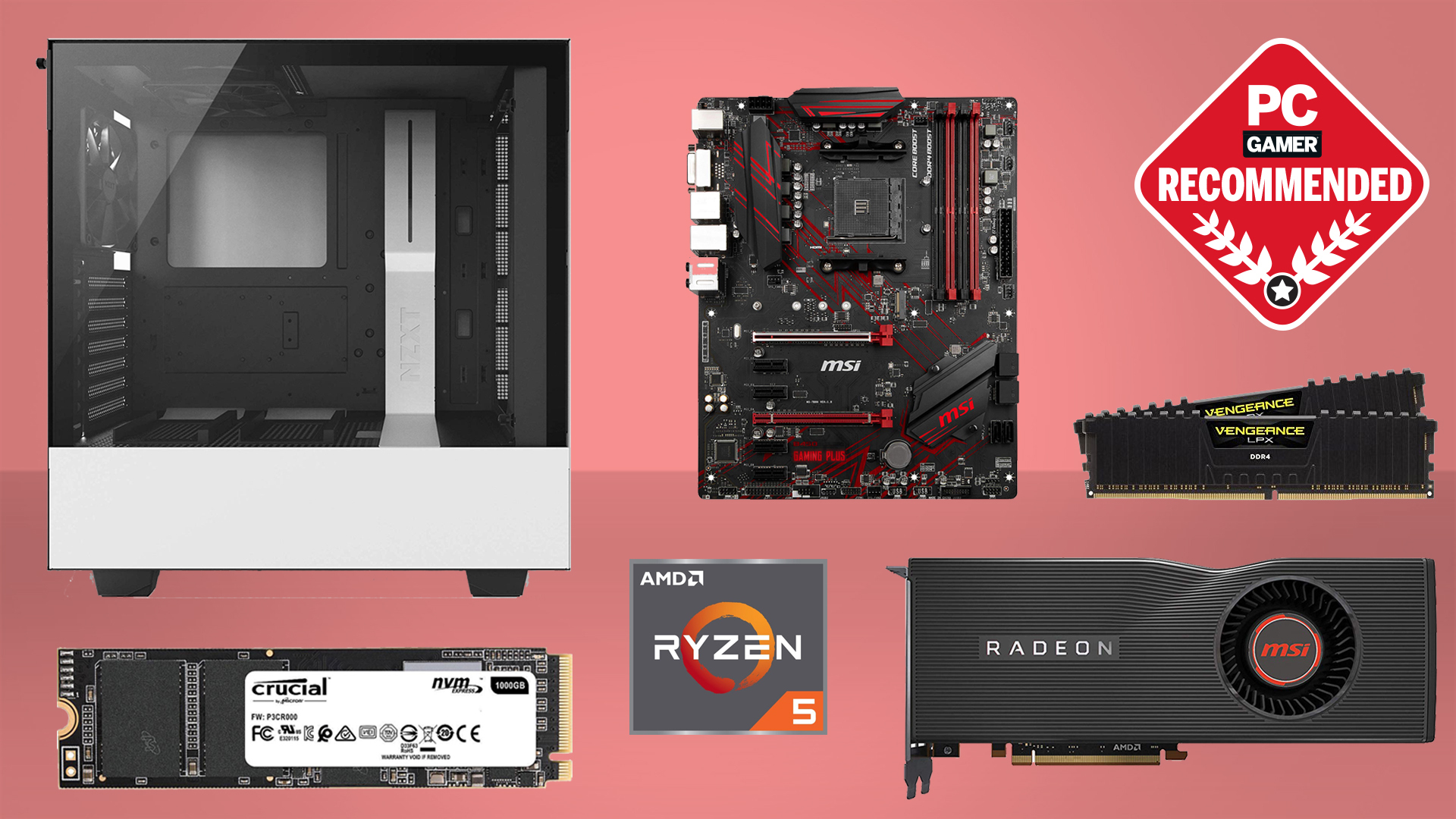
Best CPU for gaming: the top chips from Intel and AMD
Best graphics card: your perfect pixel-pusher awaits
Best SSD for gaming: get into the game ahead of the rest
Hunt also announced that HIBP is now open source via the .NET Foundation. He said this is the right move for the longevity of the project, and that it ensures a more sustainable future rather than having the service be solely dependent on him. It's also important for the purpose of transparency.
"Putting the code out there in public goes a long way to addressing concerns people have about the way the service operates. For example, people have often questioned whether I'm logging searches in order to build up a new list of email addresses," Hunt explained in a previous blog post. "No, I'm not, but at present that assertion effectively just boils down to 'trust me'. Showing the code—the actual code—and demonstrating that things aren't logged is a very different proposition," Hunt said.
These are both welcome announcements, and should ensure that HIBP remains a relevant and useful service for a long time to come.

Paul has been playing PC games and raking his knuckles on computer hardware since the Commodore 64. He does not have any tattoos, but thinks it would be cool to get one that reads LOAD"*",8,1. In his off time, he rides motorcycles and wrestles alligators (only one of those is true).

 Join The Club
Join The Club












