How to protect your privacy and PC online
ISPs can do what they want with your personal data. Here's how you can fight back.

This guide was originally published in 2017, and has been updated with new tips.
Net neutrality is dead, and with it, some of the protections American citizens had against ISPs taking advantage of their data. And we don't just have to worry about privacy while we browse the web: it's common for today's games to talk to online servers and collect data about us, even when they're singleplayer.
It's a fact of modern Internet existence that we give up data in exchange for services (think Google and Facebook), but all too often we don't even realize that data is being collected. And having your data collected by an Internet Service Provider is something different: we're not making the same choice, because without an ISP you can't get online at all. Your wireless provider, cable company, or copper-wire telco generally set prices in a vacuum and are the first gatekeepers between you and your Steam account.
If you're not too keen on companies scooping up your data, there are some things you can do to protect your privacy. There are also some common practices that don't do much at all—it's important to know what works and what doesn't when it comes to protecting yourself online.
Know your priorities
Protecting your privacy and securing your identity can very easily take you down a rabbit hole of computer science paranoia. Instead of mulling over what algorithms are going to break in the next ten years, you'll benefit a lot more from concentrating on what your actual priorities are.
The first thing to do is know your adversary. Who, exactly, are you trying to protect your data from? If it's a person who might be trying to break into your email account, that takes one set of privacy and security measures. If you're looking to keep companies from selling your data, that's another set of priorities. If you're looking to evade a government's surveillance, you'll have to work a lot harder to keep yourself invisible online.
Keep up to date with the most important stories and the best deals, as picked by the PC Gamer team.
In this guide, I'm going to focus on keeping data out of the hands of companies who might want to resell it.
Incognito mode and Private Browsing aren't enough
Private Browsing (Firefox) or Incognito Mode (Chrome) may make you feel safe, but they actually don't do much to stop companies from tracking you. These browser features basically open up fresh tabs or windows without access to your history, cookies, or cache. If you're usually logged into Google or Facebook, using Incognito Mode or Private Browsing will basically treat your browsing session as though you're not logged into anything, and will clear any accumulated cookies or cache when the windows is closed. Just like any other session, a service can track you the minute you log in.
This mode is really useful when using public computers (like at a library or school campus). But if you're trying to keep ISPs from snooping, it won't help at all. Additionally, if you use Google for a search, Google can still use some information about you (search terms, geolocation, time of day), though it generally won't be tied to your identity. That is, unless you use it at home.
A recent addition to Firefox's Private Browsing includes a tracking protection feature similar to Privacy Badger, an add-on from the Electronic Frontier Foundation that "stops advertisers and other third-party trackers from secretly tracking where you go and what pages you look at on the web."
Do Not Track
Most modern browsers now come with a 'Do Not Track' signal that they can send to websites with every request. While DNT is often hidden in the options of your browser, enabling it lets a web server know that you don't want cookies served up that can be used to track you. It's a good step forward, and is generally transparent to the user.
Here's how to enable it:
- Chrome: Settings > Advanced Settings > Privacy and Security, toggle on "Send a 'Do Not Track' request with your browsing traffic"
- Firefox: Options > Privacy > Click "manage your Do Not Track settings" > Click "Always apply Do Not Track"
- Check this article for other browsers
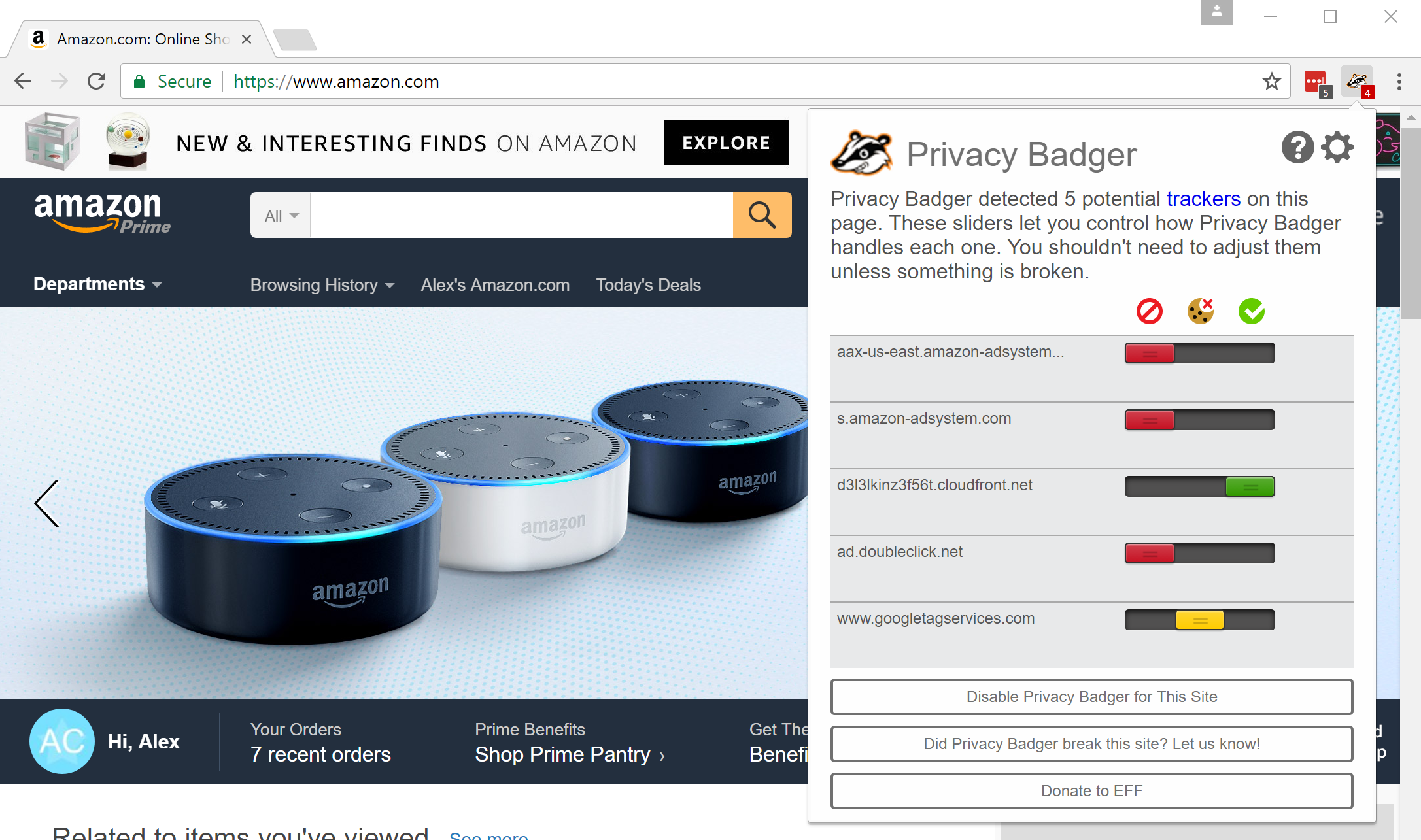
Get Privacy Badger
One of my favorite browser extensions is Privacy Badger, mentioned earlier. Privacy Badger is open source, which means there's no proprietary secret code you have to worry about. Second, Privacy Badger is holistic. It will look for code, cookies, and other things that look like they're trying to track you and block them out. A system of sliders allow you to set what's allowed and what's not.
While Privacy Badger is awesome, some websites are so full of advertising code and scripts that it can be hard to sort out the good from the okay from the bad. On numerous occasions, Wired's website has ceased to work when attempting to read a story while I had Privacy Badger turned on. Only by temporarily disabling it was I able to read the story.
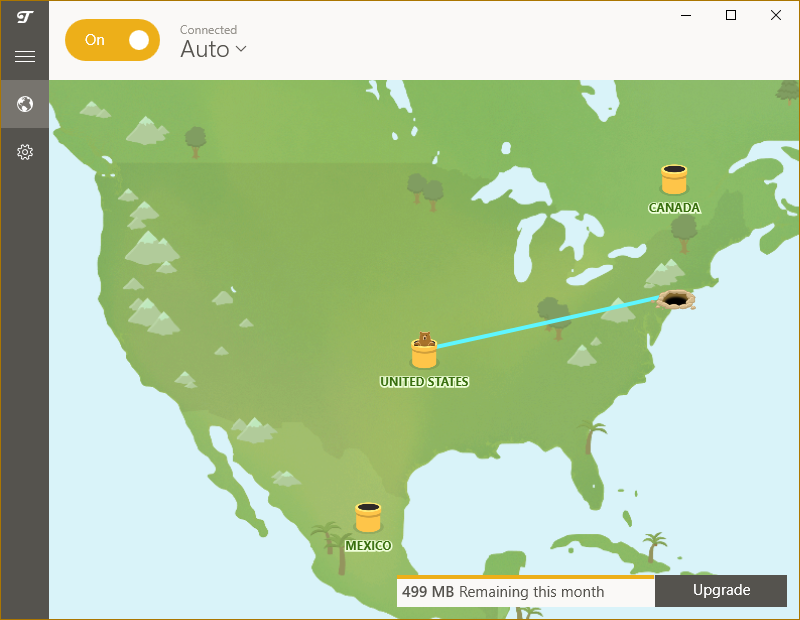
A good VPN is your friend
Your first real tool in the privacy battle is the trusty virtual private network (VPN). A VPN is an encrypted connection that allows you to connect to a network over the internet in a way that treats your connection as though you were a part of that local area network (LAN). A VPN is really useful for companies, as workers can access shared drives, printers, and other resources from home. It's also a great privacy tool.
Since a VPN provides an encrypted tunnel to a remote location, the traffic between your PC and the VPN cannot be read by an intermediary. However, any unencrypted internet traffic going in and out of the VPN could still be intercepted and deciphered. Additionally, all of your outgoing traffic will appear to come from the VPN server's IP address. This makes the VPN an ideal method for getting around censorship and hiding most of your internet traffic. This is also why I recommend using a VPN when connecting to any open Wi-Fi hotspot, since open Wi-Fi does not encrypt your internet traffic.
There are plenty of pitfalls when dealing with VPNs, though. The first and most important thing to know is that a VPN provider can see all of your traffic. Needless to say, while you can use your employer's VPN to hide your IP from your home, your employer can see everything you do while connected to it, so act accordingly.
When you're using a third party VPN provider, you're offloading trust from your ISP and placing it onto your VPN provider. VPN providers are no more regulated than any other web service you might use, so it behooves you to read up on a provider's privacy policy. (Yeah, the fine print stuff that you always skip and just click "agree".)
When choosing the best VPN, look for VPNs that don't log traffic, and don't retain or sell any data. Generally, all VPNs will have to respond to requests from law enforcement. However, a VPN provider that doesn't keep logs won't have much to show when authorities come knocking. I personally use Private Internet Access, but do your own research and read over privacy policies before choosing a provider.
You may be able to use a VPN for gaming, but some providers only allow traffic on commonly used internet ports (like HTTPS or IMAP, for instance). When choosing a VPN, be sure to find out if they open up TCP and UDP ports that games may need to communicate. Also, keep in mind that using a VPN while gaming can introduce latency.
Finally, the IP addresses of VPN providers are widely known, so a web service will know if you're connecting via a VPN.
Tor
The Tor browser has widely been touted as a method to secure your browsing. Tor is short for The Onion Router, and basically hides your IP by relaying your web requests through a network of proxy servers called relays or nodes. When accessing a website outside of the Tor network (all Tor sites end in .onion), the only node that can see the outgoing traffic is called an exit node, which makes the request to the appropriate site (like google.com).
Tor is a great method for browsing anonymously, so long as you're not trying to do something that would send the FBI right to your door. Since Tor is open source and anyone can operate a Tor node, you better believe the U.S. government (and presumably others) operate Tor exit nodes. On top of that, using Tor can raise eyebrows from governments, which can attract closer scrutiny of traffic. Of course, the more people that use Tor for not-so-shady browsing, the less scrutiny it will warrant.
As long as you're not trying to sell drugs or look up child pornography, using Tor is generally a good way to keep yourself anonymous. To use Tor, you'll need the Tor browser, which is basically a modified version of Firefox. The Tor browser comes standard with Tails, a Linux distribution built for anonymity and security.
Keep that PC clean
Although I can't remember the last time I had one of my PCs become bogged down with porno popups, malware is another thing to keep on the lookout for. Instead of selling you live sex shows, today's malware aims to read your browsing data and resell it to third parties.
By keeping your anti-malware software up-to-date, you can reduce the chance of having your PC infected by this stuff. You should also keep your system updated with the latest Windows updates and browser software. Both Mozilla and Google are very proactive about keeping their browsers secure, and keeping them updated means that you have the latest patches to known exploits.
Review privacy policies for services and opt out
While ISPs may be able to do whatever they want for now (thanks Congress), you can still exert some control over the other services you use. Take some time to think about all the services you've signed up for. Each one of them has their own privacy policy, and by using that service you're agreeing to it.
If you find yourself using a service that makes you uneasy when you look at its privacy policy, find ways to opt out. Find alternative services, where you can. Duck Duck Go, for instance, offers web search that doesn't collect personal data.
If you're lucky enough to live in a place with more than one ISP, look for alternative providers too. Here in the Bay Area, the ISP Sonic has a privacy policy that vows to never sell your personal information, and only retain connectivity logs for 14 days. (They even abide by the DNT signal from browsers.) A lot of the U.S. sadly isn't lucky enough to have several ISPs vying for their dollars, so options like this might not be available for you. We're sorry if Comcast has a monopoly in your area.

Use Firefox
I have to admit, Chromium Home is my default browser on my Linux machines, and I default to Chrome on Windows. But as far as privacy is concerned, Firefox is the winner. Unlike Google's Chrome, Firefox is completely open source, which means the entirety of its code can be inspected. While Chrome is based on the open source Chromium, Chrome can and will phone home to Google with usage statistics and other information. Opera also claims to be a privacy-focused browser and includes a free VPN built in, though it's not open source like Firefox.
If Google Chrome's privacy policy gives you the willies, consider switching.
Prefer HTTPS
Wherever you can, you should prefer HTTPS (also known as SSL or TLS) when browsing online. TLS traffic is encrypted so that only the recipient and server can see the data that's being transmitted. It's the reason why your bank's website and Amazon orders are secure. Even where security isn't paramount, more websites are starting to use TLS/HTTPS in order to simply protect users' privacy. Google thinks it's a good idea too, and started ranking HTTPS websites higher back in 2014. The EFF offers an HTTPS Everywhere browser extension that tries to use HTTPS wherever possible.
HTTPS isn't perfect, however. An ISP (or VPN provider) can see the requested URL, so HTTPS by itself doesn't ensure total privacy.
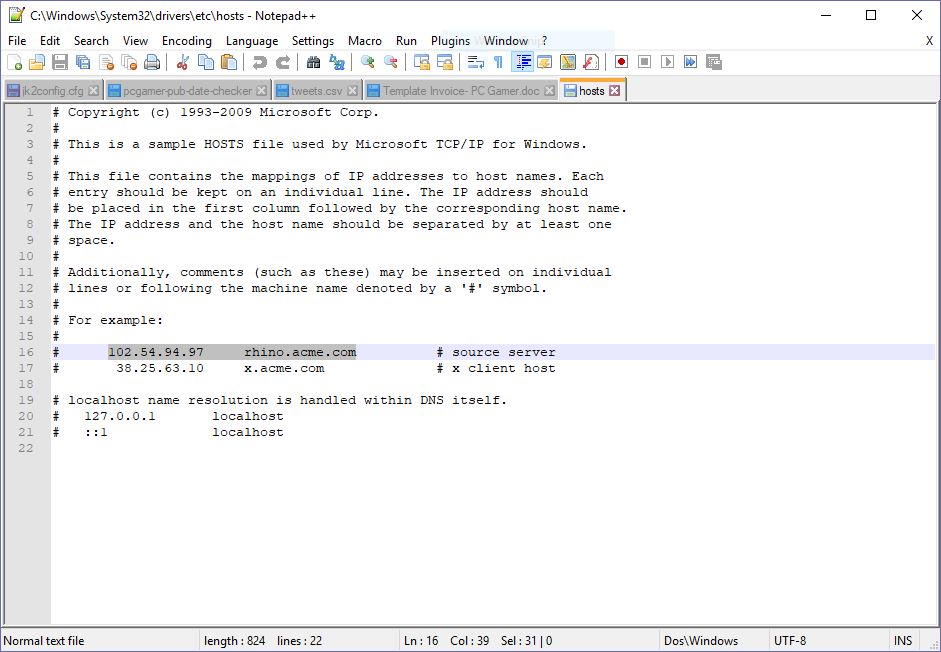
Learn how to block data collection in the Windows hosts file
Gamers concerned about Red Shell, a small service installed in some games that collects browsing data to inform the developer about player purchasing habits, have taken up a solution: blocking Red Shell in the Windows hosts file. What's a hosts file? A really simple file that's been part of Windows and other operating systems for decades that tells your PC how to convert a hostname into an IP address, just like a DNS server.
By adding the IP address 0.0.0.0 and the hostname of the service you want to block to the hosts file, you can have Windows redirect that service to your own PC, so it won't successfully talk to a remote server.
- Here's a guide to doing this for Red Shell specifically.
- Here's a great How-To Geek walkthrough on how to edit your hosts file on Windows, Linux, and Mac.
To take things a step further, check out the hosts file on the website Someonewhocares.org. It blocks an extensive list of websites, including old "shock" sites like goatse, many ad services like doubleclick and Google Analytics, and many more. This is basically a brute force form of the privacy protection added by something like Privacy Badger, and there's a good chance some websites you visit won't display properly as a result. But it's trivial to delete some or all of these hosts file modifications in Notepad if you have any issues.
Conclusion
At the end of the day, we all give up some privacy for the sake of convenience. The real trick is knowing how much you're willing to inconvenience yourself in order to retain some of that privacy. For some, going full-bore with a VPN, Tor, and being a social media hermit is the only way to go. Some people may not care at all.
Most of us will take the middle road and find a nice warm spot somewhere between the two extremes. Until we pass laws that say that user data should be private by default, read the fine print and take measures that are appropriate. Good luck out there.


