Russian hackers are using WinRAR as a 'cyberweapon' against Ukraine
Ukrainian government agencies reportedly suffer data loss due to Russian operatives.

Ukrainian authorities are reporting that Russian hackers have used the WinRAR file compression tool to wipe data from computers at multiple government agencies.
The Ukrainian Government Computer Emergency Response Team (CERT-UA) claims (via Bleeping Computer) that Russian hackers, possibly the infamous Sandworm group, acquired compromised VPN accounts which in turn provided access to official Ukrainian state networks.
The hackers apparently used the RoarBAT script, which searches for files on the targeted machine with extensions including .doc, .docx, .rtf, .txt, .xls, .xlsx, .ppt, .pptx, .jpeg, .jpg, .zip, .rar, .7z, and several more, before archiving the files with WinRAR and applying the the "-df" option. Using this option automatically deletes the source files after archiving. The RoarBAT script then deletes the archived files, leading to total data loss.
The hack is possible thanks to the ubiquity of WinRAR on modern PCs. Apparently, Linux systems are not immune from the attack and can be compromised using a BASH script and the standard dd utility, whatever any of that means.
Ukraine's CERT-UA says this latest hack is suspiciously similar to another attack earlier this year on the Ukrainian state news agency "Ukrinform" earlier this year which was attributed to the Sandworm group.
"The method of implementation of the malicious plan, the IP addresses of the access subjects, as well as the fact of using a modified version of RoarBat testify to the similarity with the cyberattack on Ukrinform," says CERT-UA.
Unsurprisingly, it also says that all Ukrainian government operatives should tighten up on their VPN security via enabling multi-factor authentication. Which is probably a lesson for all of us, too.
Keep up to date with the most important stories and the best deals, as picked by the PC Gamer team.
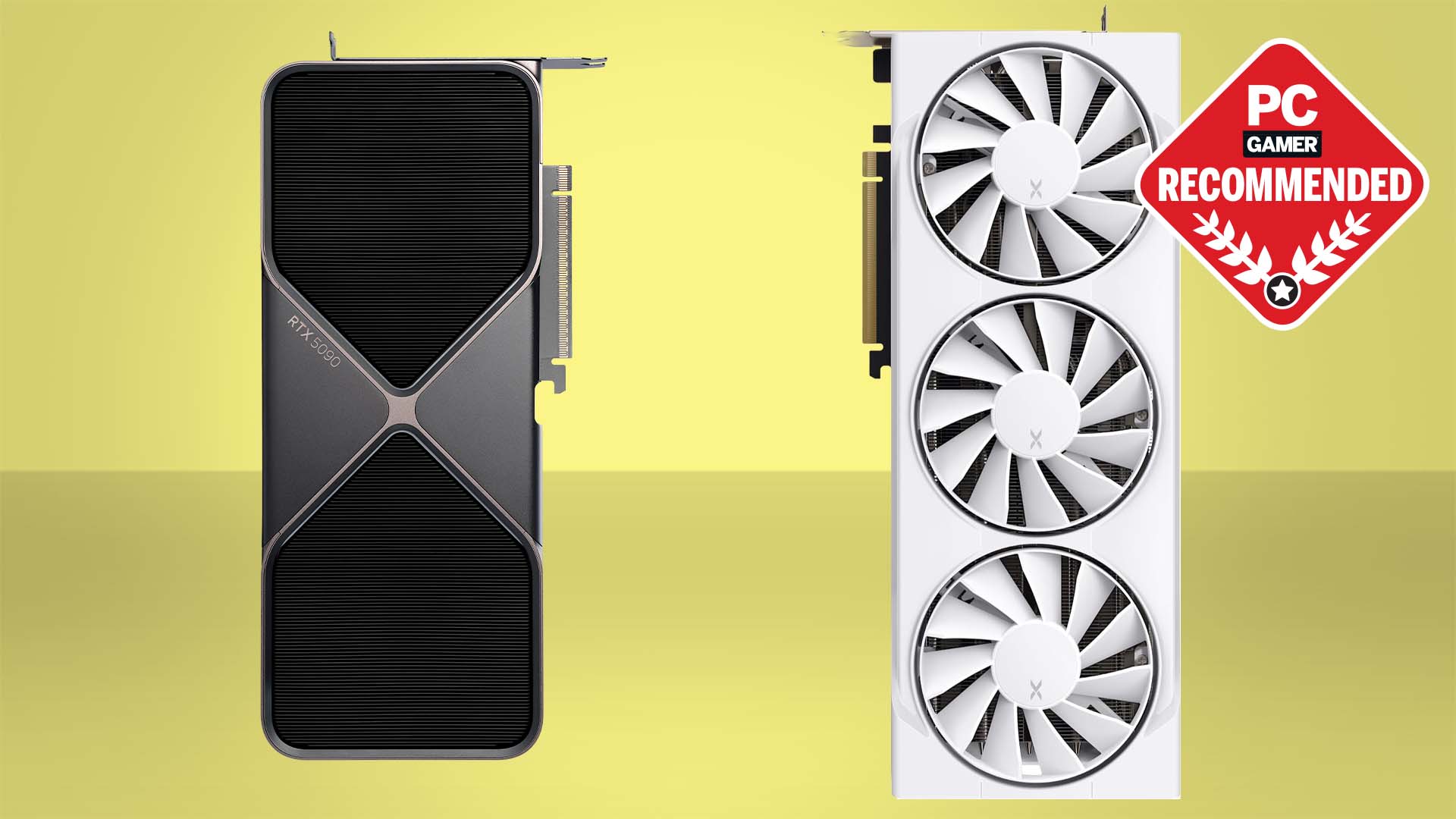
Best gaming PC:
The top pre-built machines from the pros
Best gaming laptop:
Perfect notebooks for mobile gaming

Jeremy has been writing about technology and PCs since the 90nm Netburst era (Google it!) and enjoys nothing more than a serious dissertation on the finer points of monitor input lag and overshoot followed by a forensic examination of advanced lithography. Or maybe he just likes machines that go “ping!” He also has a thing for tennis and cars.