Researchers discover first-ever rootkit that targets modern UEFI motherboards
The rootkit is based on a vulnerable version of the LoJack recovery software for laptops.
Keep up to date with the most important stories and the best deals, as picked by the PC Gamer team.
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
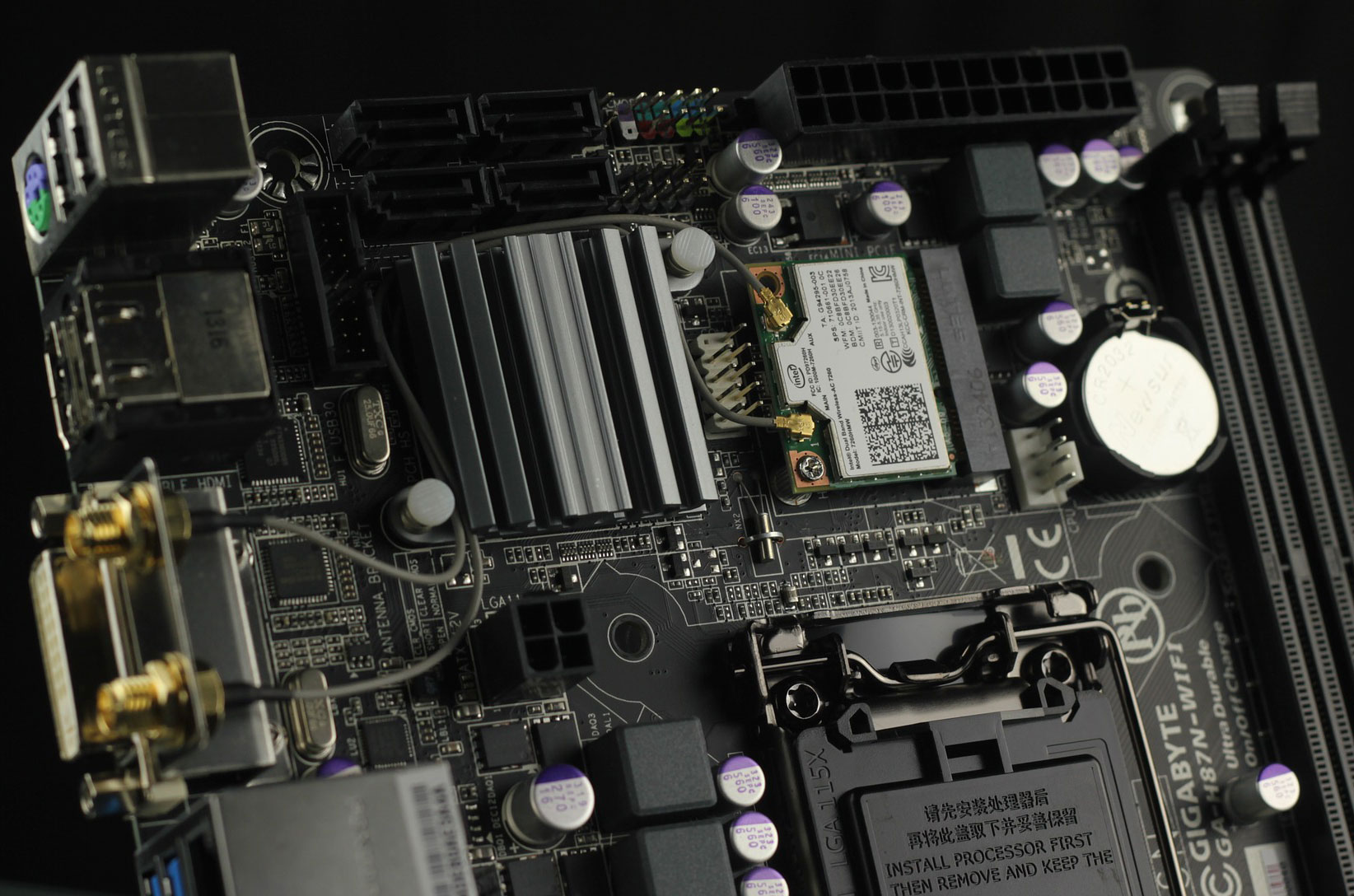
Security researches say they've discovered the first known instance of a rootkit that targets the Windows Unified Extensible Firmware Interface (UEFI), which is that bit of code on newer versions of the best gaming motherboards that many people still refer to (incorrectly) as the BIOS.
UEFI firmware has largely replaced the traditional BIOS, or Basic Input/Output System, because it has several advantages—it offers a slicker interface that makes navigating settings easier, it allows systems to boot from larger storage drives, and most importantly, it's more secure. How To Geek has a pretty good breakdown of the differences between UEFI and traditional BIOS chips, but those are the main points.
Rootkits are types of malware that attack systems at deep levels. There are different kinds of rootkits, which are typically difficult to detect and remove, in part because they load before the operating system.
Article continues belowDuring a recent security conference, Frédéric Vachon, a malware researcher at ESET, talked about the discovery of the first-ever instance of a rootkit in the wild that has targeted UEFI systems in successful attacks.
"UEFI rootkits have been researched and discussed heavily in the past few years, but sparse evidence has been presented of real campaigns actively trying to compromise systems at this level," Vachon said.
Researchers named the rootkit LoJax because it's based on a compromised version of Absolute Software's LoJack recovery software, which is supposed to help victims of stolen laptops to silently track and locate their pilfered system.
LoJack makes this possible by executing code before the OS loads, and before any antivirus software is launched. So even if a thief replaces the stolen laptop's storage drive, LoJack will still ping its location to the rightful owner.
Keep up to date with the most important stories and the best deals, as picked by the PC Gamer team.
The same goes for LoJax, which is based on a vulnerable 2009 version of LoJack that is easily altered. As with many strains of malware, deploying it starts with a phishing email or otherwise tricking a user into downloading and installing a dropper agent.
"Once I have a foothold on the machine I can use this tool to deploy the UEFI rootkit," Vachon explained.
ESET actually wrote about this in September of last year. At the time, ESET noted that some UEFI rootkits have been presented as proofs of concept, while others are known to be used by government agencies.
"However, no UEFI rootkit has ever been detected in the wild—until we discovered a campagn by the Sednit APT group that successfully deployed a malicious UEFI module on a victim's system," ESET said.
It's known that Sednit agents were developing LoJax as far back as May of last year, but September was the first time it was spotted in live campaigns. Hopefully this doesn't become a trend in 2019.

Paul has been playing PC games and raking his knuckles on computer hardware since the Commodore 64. He does not have any tattoos, but thinks it would be cool to get one that reads LOAD"*",8,1. In his off time, he rides motorcycles and wrestles alligators (only one of those is true).

 Join The Club
Join The Club