AMD, Nvidia, and Intel GPUs could be capable of hosting malicious code
A hacker has reportedly sold a technique for hiding malicious code and executing it on a GPU.
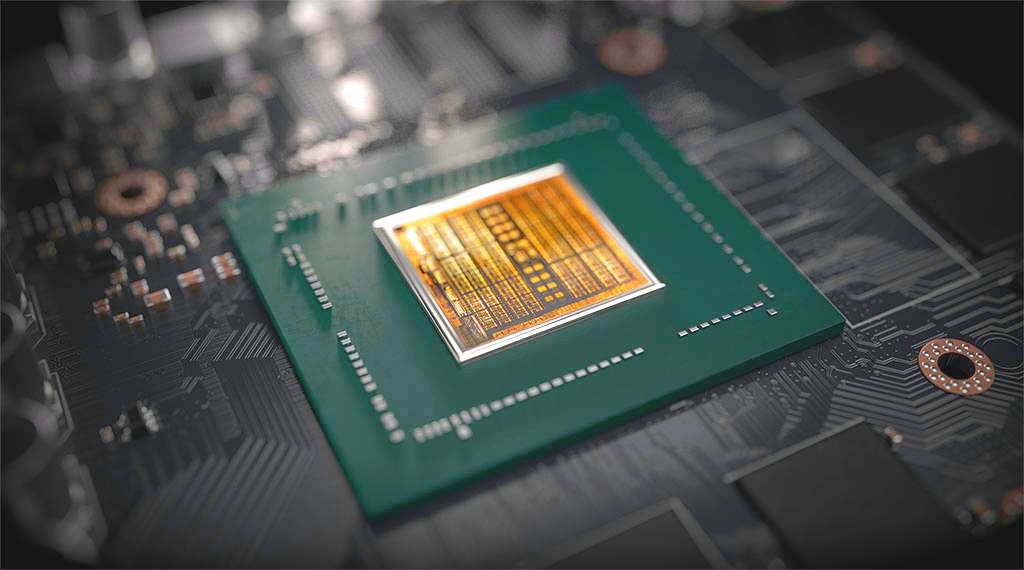
Hackers may have figured out a way to store and execute malicious code on a graphics card, potentially allowing it to avoid detection by antivirus software. The code has also reportedly been sold via a hacking forum, and so far we've no further indication of how dangerous the technique could be.
Code that sits undetected in GPU memory is likely very dangerous due to the potential difficulty associated with removing it, which could rely on flashing the GPU entirely—an already risky affair. However, the overall threat of the reported method will depend on what it takes to implant the code into GPU memory to begin with.
All we know of the technique, however, is what a hacker, who reportedly later sold it, said of it on a forum. This was later spotted and reported by Bleeping Computer.
The original forum post reads:
"Sell PoC [proof-of-concept] of technique that avoid AV detects from RAM scanning. It allocates address space in GPU memory buffer, inserts and executes code from there."
The post then explains that the technique works only on Windows machines that support OpenCL 2.0 or higher—an open standard used to accelerate applications on GPUs. Also that the technique has been tested on Intel UHD 620, UHD 630, Radeon RX 5700, GeForce GTX 740M, and GeForce GTX 1650 graphics cards.
The possibility of this technique working on both AMD and Nvidia discrete GPUs would be worrying enough alone. However, the possibility of it also working across Intel iGPUs would potentially open up a much larger percentage of PCs to the exploit.
As Bleeping Computer notes, VX-Underground, which calls itself the "largest collection of malware source code, samples, and papers on the internet", is aware of such a technique and will demonstrate it soon.
Keep up to date with the most important stories and the best deals, as picked by the PC Gamer team.
Recently an unknown individual sold a malware technique to a group of Threat Actors.This malcode allowed binaries to be executed by the GPU, and in GPU memory address space, rather the CPUs.We will demonstrate this technique soon.August 29, 2021
Best CPU for gaming: the top chips from Intel and AMD
Best graphics card: your perfect pixel-pusher awaits
Best SSD for gaming: get into the game ahead of the rest
This isn't the first time a GPU, and potentially OpenCL, have been used to execute malicious code. Various users point to a similar PoC called Jellyfish, which is a Linux-based GPU rootkit that works on both Nvidia and AMD GPUs and requires OpenCL drivers to function. This code hasn't been touched in six years, though its creators note that such GPU-based malware benefits from the lack of tools and software able to detect them.
Jellyfish and the more recent technique are said to differ, however, at least according to the seller of the potentially harmful PoC.
It's possible that we'll see further efforts to take advantage of GPU memory, or accelerators in general, considering their prominence in all manner of machines today. That said, there's little doubt in my mind that many exploits exist in computing at any one moment, and while manufacturers wrestle with plugging up holes in their code, it's just as important you do all you can to keep your system safe.
Usually, that means not giving malicious actors a chance to download code onto your system, after which they can usually wreak all sorts of havoc often undetected.

Jacob earned his first byline writing for his own tech blog. From there, he graduated to professionally breaking things as hardware writer at PCGamesN, and would go on to run the team as hardware editor. He joined PC Gamer's top staff as senior hardware editor before becoming managing editor of the hardware team, and you'll now find him reporting on the latest developments in the technology and gaming industries and testing the newest PC components.