Researchers allegedly discover 13 major security flaws specific to AMD's Zen CPUs
The newly discovered flaws appear similar in severity to Spectre and Meltdown.
Update: Are these vulnerabilities real or imagined, and how severe are they really? Following our initial report, some of the claims have been called into question. The flaws may be real, but taking advantage of the flaws in many cases appears to require root/admin access, which typically means a system is already severely compromised.
Original story:
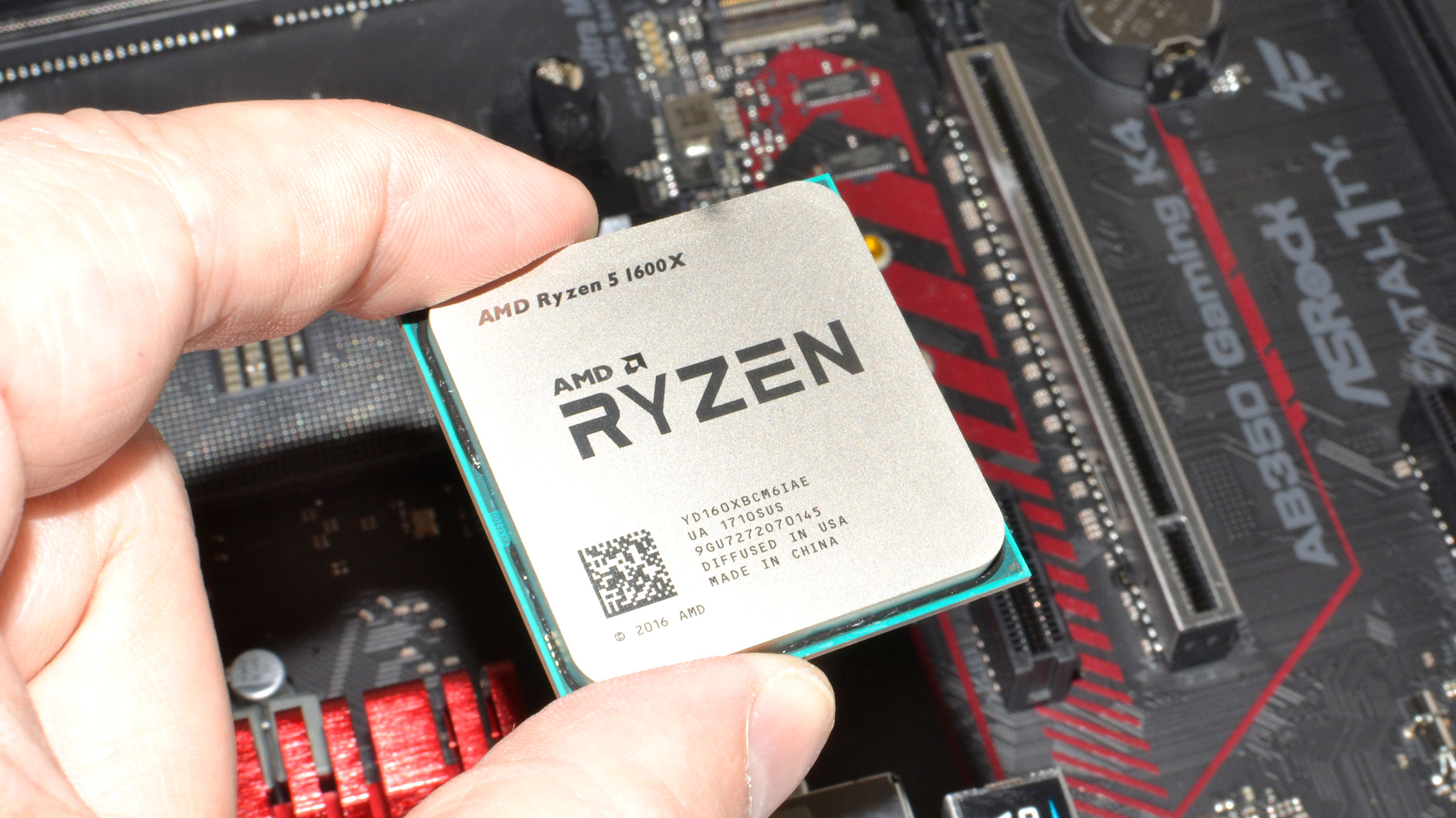
Hot on the heels of Spectre and Meltdown, researchers say they have discovered more than a dozen (or exactly a baker's dozen) new critical security flaws affecting AMD's Ryzen and Epyc processor lines, CNET reports. The vulnerabilities purportedly lie in what is supposed to be a secure part of the processors where sensitive information is contained.
The alleged flaws were discovered by CTS-Labs, a security outfit in Israel. Unlike Google's Project Zero team, which alerted chipmakers months in advance to Spectre and Meltdown before disclosing them to the public, CTS-Labs gave AMD less than 24 hours to look at its findings and respond before publishing the details. AMD is in the process of investigating the matter.
"At AMD, security is a top priority and we are continually working to ensure the safety of our users as new risks arise. We are investigating this report, which we just received, to understand the methodology and merit of the findings," an AMD spokesman said.
It's not yet clear how serious these newly discovered flaws are. As presented, the 13 flaws fall into four categories called MasterKey, Ryzenfall, Fallout, and Chimera. Between the four main vulnerabilities, an attacker could supposedly bypass a Ryzen or Epyc CPU's secure boot and install malware into the BIOS, and then onto the processor itself. They could also potentially leverage a pair of manufacturer backdoors to compromise a system's firmware and chipset.
If the vulnerabilities are as widespread and critical as CTS-Labs presents them to be, there are all kinds of implications and potential scenarios. Collectively, the vulnerabilities could open customers up to covert and long-term industrial espionage, sophisticated malware attacks that expose passwords and other personal information, hardware-based ransomware, and more.
Keep up to date with the most important stories and the best deals, as picked by the PC Gamer team.
The industry at large is still reeling from Spectre and Meltdown. Some of the early patches have caused a few headaches, such as random reboots and performance degradation. It remains to be seen what the fallout might be like for the flaws CTS-Labs claims to have found.

Paul has been playing PC games and raking his knuckles on computer hardware since the Commodore 64. He does not have any tattoos, but thinks it would be cool to get one that reads LOAD"*",8,1. In his off time, he rides motorcycles and wrestles alligators (only one of those is true).

 Join The Club
Join The Club












