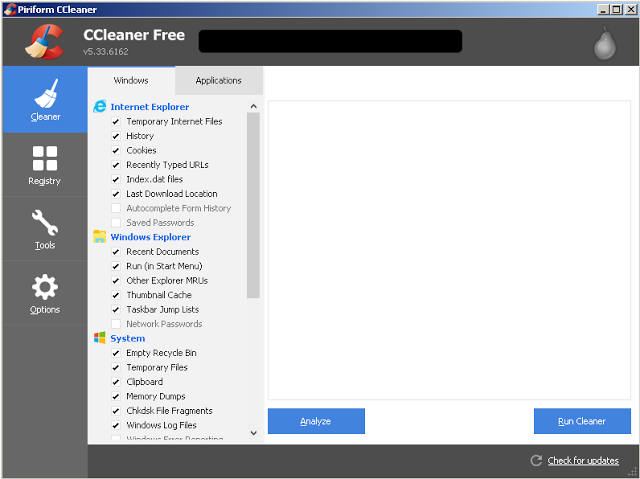
Hackers use CCleaner as malware host, affects 2.27 million users
The security app distributed malware for four weeks.
Around 2.27 million users of Piriform's popular CCleaner security app have been advised to update the application—a result of sophisticated hacker-hidden malware. Discovered by researchers at Cisco's Talos division, hackers are thought to have run code from a remote IP address using a backdoor.
Piriform, owned by security firm Avast, says up to three percent of its customers could have been affected after using CCleaner 5.33 (offered for download between August 15 and September 12), and CCleaner Cloud 1.07 (launched on August 24).
"The compromise could cause the transmission of non-sensitive data (computer name, IP address, list of installed software, list of active software, list of network adapters) to a third party computer server in the USA," said Piriform in this blog post. "We have no indications that any other data has been sent to the server… We are continuing to investigate how this compromise happened, who did it, and why. We are working with US law enforcement in their investigation. A more technical description of the issue is on our Piriform blog."
In a separate post, Talos reports: "In analyzing DNS-based telemetry data related to this attack, Talos identified a significant number of systems making DNS requests attempting to resolve the domains associated with the aforementioned DGA domains. As these domains have never been registered, it is reasonable to conclude that the only conditions in which systems would be attempting to resolve the IP addresses associated with them is if they had been impacted by this malware."
Piriform adds that it's also working with third-party sites to remove the compromised versions of CCleaner, and that all users should update to its latest CCleaner 5.34 version right away.
Keep up to date with the most important stories and the best deals, as picked by the PC Gamer team.

 Join The Club
Join The Club