Watch out for phishing emails linking to fake Meltdown and Spectre patches
Don't take the bait.
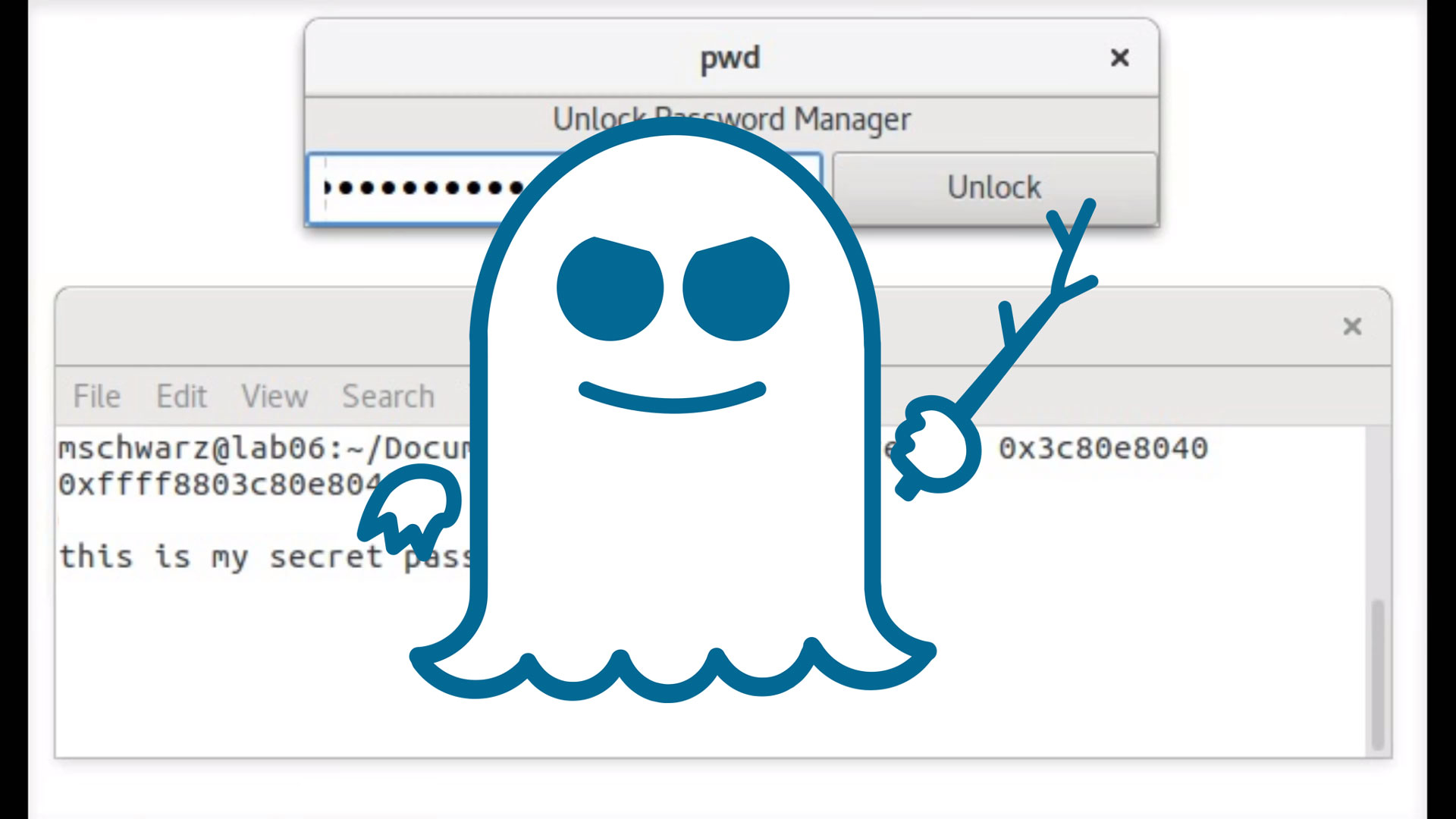
Now is a good time to double down on safe computing practices, and to remind family and friends to do the same. That's because fake patches for Meltdown and Spectre that contain malware have created a need to be extra cautious.
It was only a matter of time before this happened. According to Malwarebytes, it already has. The security outfit says it identified a recently registered domain purporting to be an official security portal in Germany, but actually links visitors to malware.
The site is not actually affiliated with any official government entity, it just looks like one. Visitors who stumble upon it, mostly likely through a phishing email, are encouraged to download a ZIP archive that is presented as a security patch for Intel and AMD systems. In actuality it's a piece of malware.
"Upon running it, users will infect themselves with Smoke Loader, a piece of malware that can retrieve additional payloads. Post-infection traffic shows the malicious file attempting to connect to various domains and sending encrypted information," Malwarebytes explains.
Malwarebytes reported the site to Comodo and CloudFlare, and within minutes of doing so it was taken offline. Unfortunately, you can bet other similar sites will appear soon, if not already.
"Online criminals are notorious for taking advantage of publicized events and rapidly exploiting them, typically via phishing campaigns. This particular one is interesting because people were told to apply a patch, which is exactly what the crooks are offering under disguise," Malwarebytes added.
Malwarebytes also warns that just because a site is using HTTPS doesn't necessarily mean it's trustworthy. The certificate just means that data between your PC and the site is secure, not that the content on the site is legitimate.
Keep up to date with the most important stories and the best deals, as picked by the PC Gamer team.

Paul has been playing PC games and raking his knuckles on computer hardware since the Commodore 64. He does not have any tattoos, but thinks it would be cool to get one that reads LOAD"*",8,1. In his off time, he rides motorcycles and wrestles alligators (only one of those is true).

 Join The Club
Join The Club












