How to check CPU and system speed after the vulnerability fixes
See the effect Meltdown and Spectre have had on your PC.
InSpectre Simple program that toggles Spectre and Meltdown protection on/off. Get it here.
X264 Benchmark V5.0 For stress-testing your CPU via 1080p video encoding. Download it here.
They sound like Bond movies—actually, one of them was a Bond movie—but in a computing context, Meltdown and Spectre are nothing like as much fun. The pair of exposed and fearfully publicized CPU vulnerabilities caused much gnashing of teeth earlier in 2018, due to the potential for hackers to target two decades' worth of processors. Teeth were gnashed even harder when the patches that Intel and AMD rolled out to fix these vulnerabilities were reported to decrease system performance.
The extent of that performance hit isn't certain, though, and varies depending on your CPU model, your OS, your storage devices, and several other factors—which is why it's time to roll up the metaphorical sleeves, and do some testing. Using a tiny app that toggles Meltdown and Spectre protection on and off by enabling or disabling their associated patches, and running some CPU benches in both environments, you'll get an understanding of the hit your system took to keep you safe. Note that we don't recommend leaving the patches disabled simply to restore that lost performance—what's a few frames per second when your personal data is up for grabs, really? This is purely an exercise in assessing the damage—gulp.
Allow Meltdown and Spectre updates
As obvious as this sounds, there's no point running CPU benchmarks to check how your performance has been affected by patches you may not even have installed yet. So, let's make sure you have the appropriate patches and firmware.
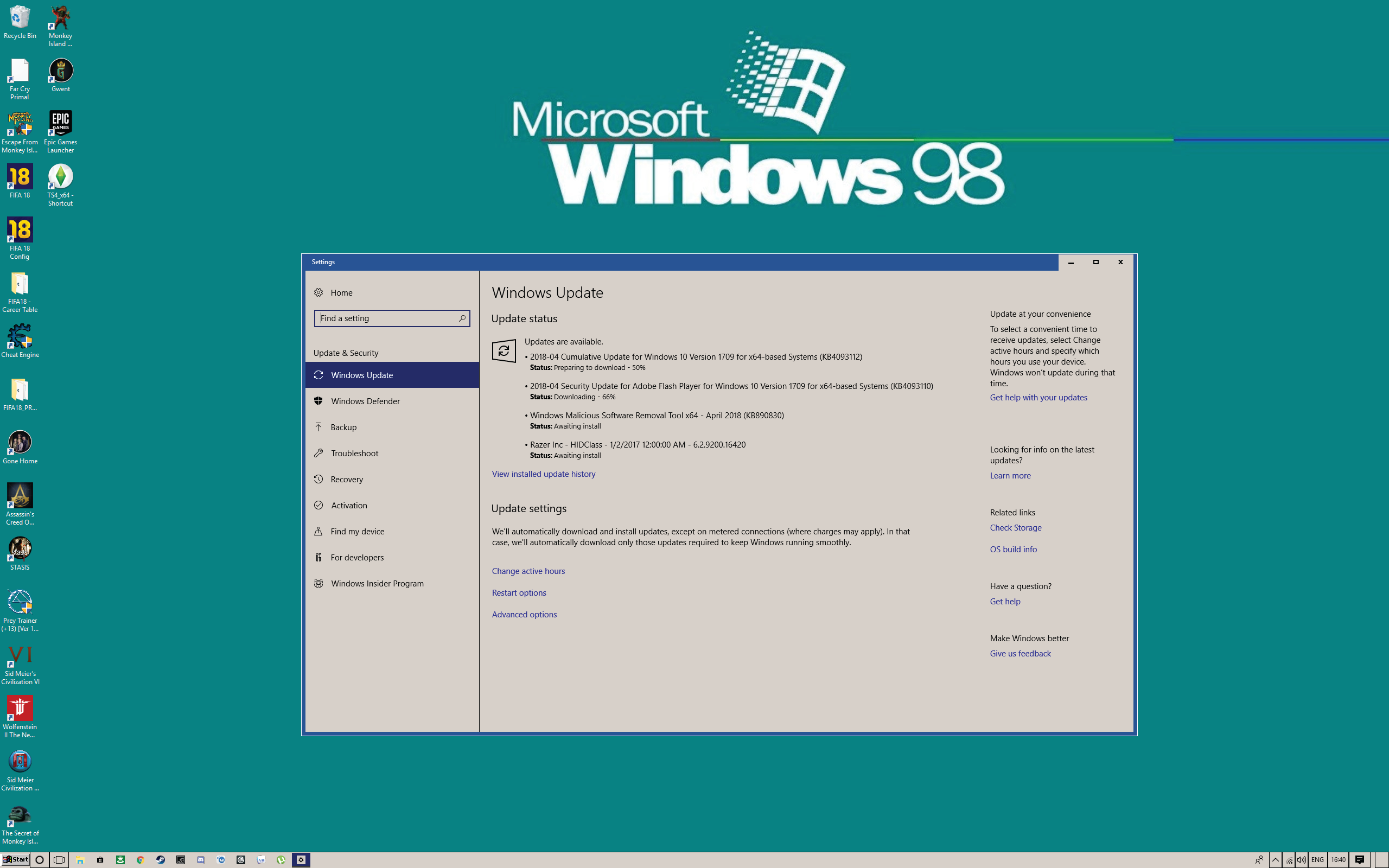
Probably by now, your OS, browser, and other programs have done their business, but just in case: Navigate to the Windows Update by typing “Update” in Cortana, and clicking the program when it appears. Under “Update status,” click “Check now” to ensure you don't have any updates pending. If you do (see image above), get them installing right away. It's also worth checking that you're running the latest version of your web browser, and enabling any program updates that prompt you to install them. That includes antivirus software.
The potentially more difficult element of Meltdown and Firmware patching involves updating your system firmware, aka flashing the motherboard BIOS. Some older motherboards may not even have the required firmware updates, but Intel has committed to supporting at least 2nd Gen Core and later CPUs, but Bloomfield, Gulftown, Clarksfield and earlier processors will remain vulnerable. But just because Intel has released updated firmware for a processor family doesn't mean your motherboard vendor will take the next step of providing an updated BIOS. We've noticed that motherboards prior to 4th Gen Core (Haswell / Z87) are often left off the update lists of motherboard vendors.
Install the required software
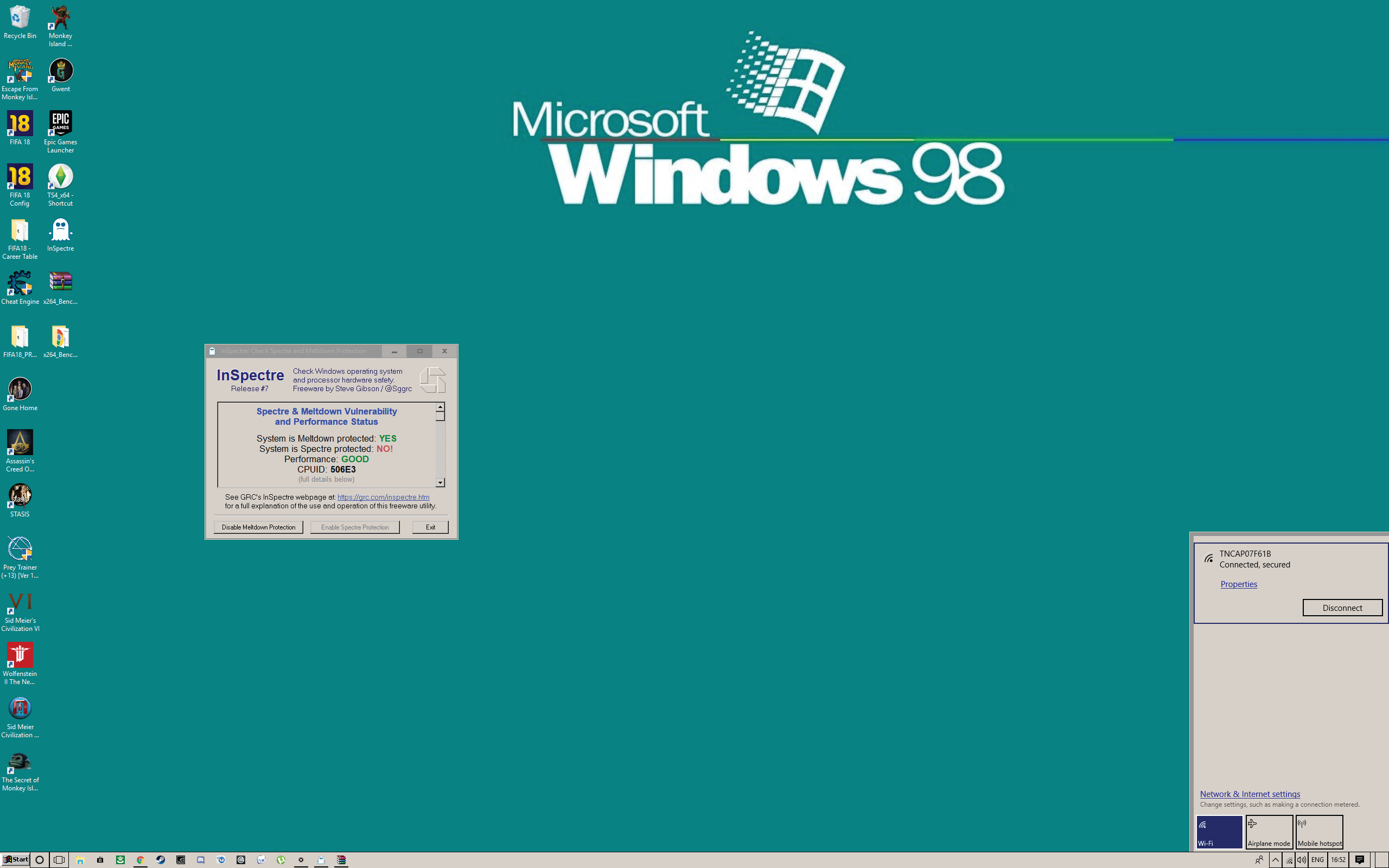
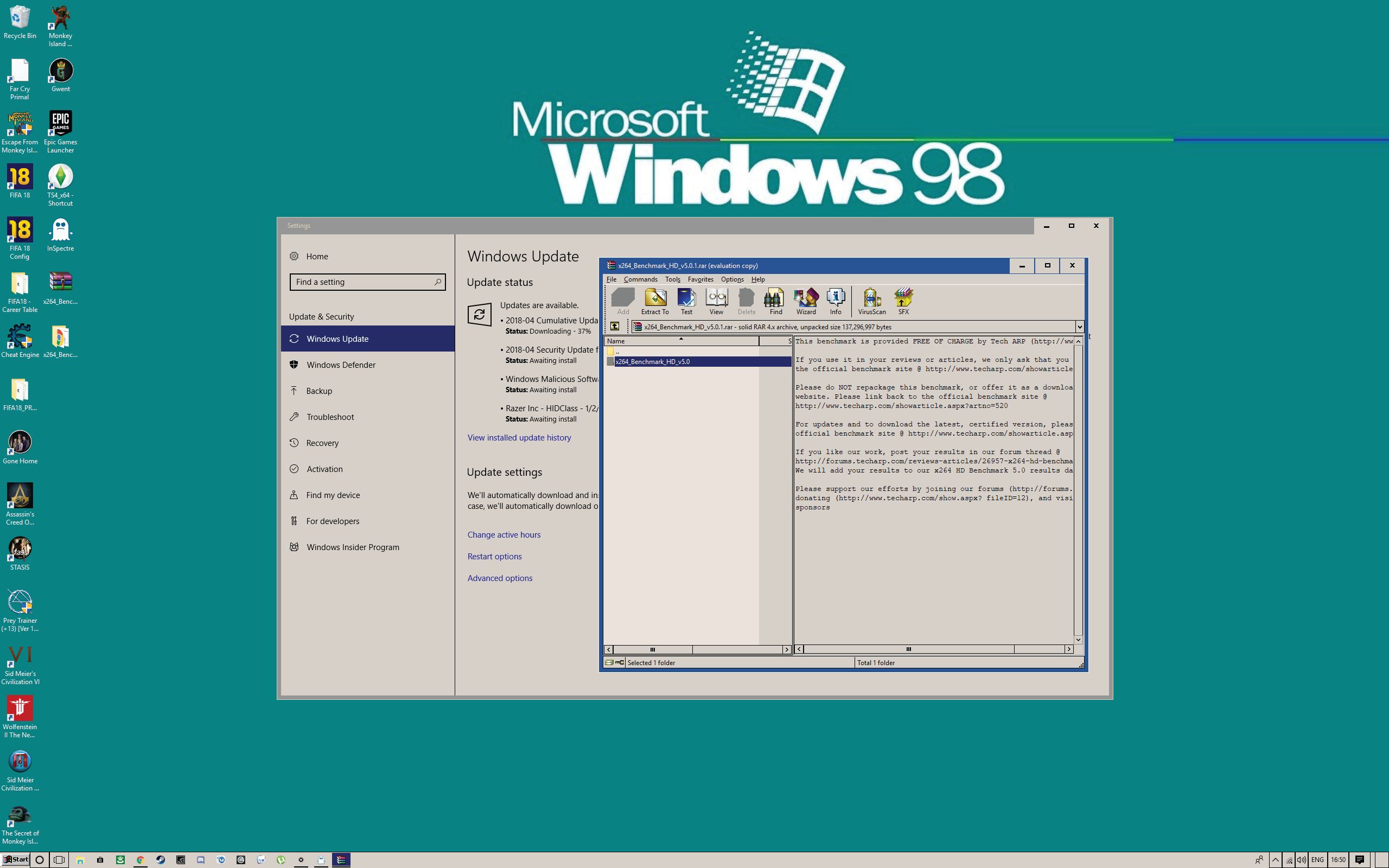
You need two programs to properly assess your before and after performance in relation to the security patches you just installed. The first, InSpectre, immediately tells you whether your system is protected against the two exploits. We're using the x264 1080p encoding benchmark (image above) to assess performance after that, but you're obviously free to use any CPU benchmark you like, as long as it spits out a number at the end that you can use to compare and contrast with other runs. If InSpectre tells you your system isn't currently protected at this point, simply repeat step 1. Do not pass “Go,” do not collect $200. Otherwise, with this and your benchmarking tool installed, you're ready to progress.
Prevent interruptions by going offline
The goal here is to run the same benchmark on the same system, under exactly the same conditions. The only variable should be whether or not your CPU security patches are enabled. In order to do so, let's eliminate the potential for Internet connection or storage drive activity to mess with the results. You never know when GeForce Experience might decide now is a good time to install new graphics drivers and plunge your screen into temporary darkness, after all. First, go offline temporarily, whether that means pulling out an Ethernet cable or USB wireless receiver, or simply disabling Wi-Fi at the bottom-right of the Start bar (see image above).
Keep up to date with the most important stories and the best deals, as picked by the PC Gamer team.
Get your storage drive fighting fit
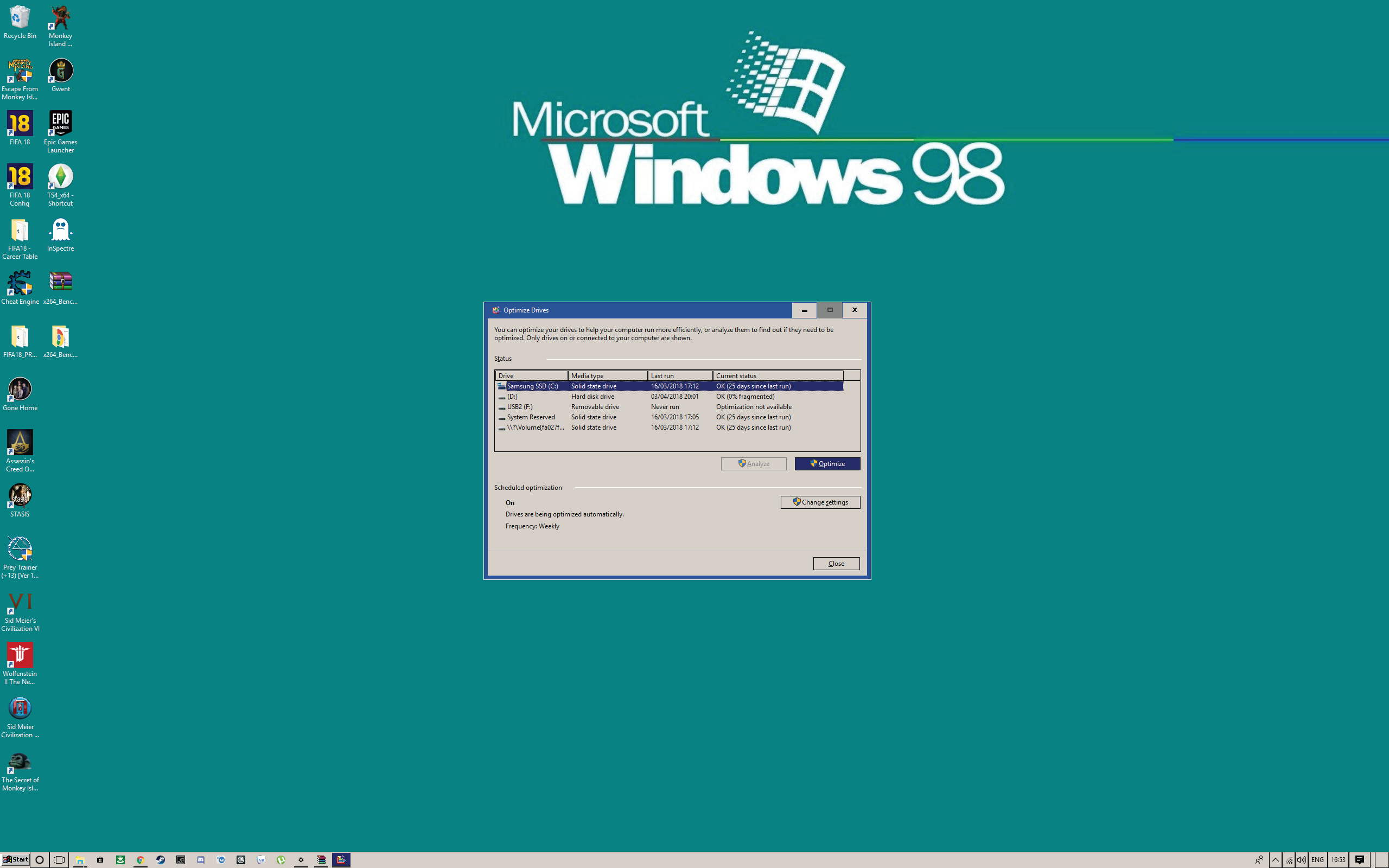
Meltdown and Spectre's fixes don't just impact CPU performance in a vacuum. Your CPU is in charge of software-defined storage (such as partitions), and the size of that workload is, most agree, affected by the security patches. All of that means that if we want our testing to be fair and accurate, we need disk activity to be the same during both test runs. That's why we've gone offline, and it's why we recommend running a TRIM on your SSD before heading to the benchmarks. Don't sweat this if Windows is installed on an HDD on your machine, because the numbers are probably so slow in the first place that performance differences will be negligible.
SSD users should right-click their primary drive in Windows Explorer, then head to “Properties > Tools > Optimize” (see image below). This starts the TRIM—it's essentially a fast defrag for solid-state drives, clearing up data cells, and tidying up where data is written. Now when you run the benchmark, you'll know that your disk isn't installing something in the background that it just downloaded online, or silted up by not having run a TRIM command for too long.
Benchmark, then benchmark again
Now's the time to actually collect the data you can use to analyze any performance hit. You can do the following procedure in any order, but for simplicity's sake, we'll run the first benchmark with Meltdown and Spectre patches disabled.
Open InSpectre to do this, and click that ominous “Disable Meltdown Protection” button in the bottom-left of the program. Then, having summoned the courage once more, click the “Disable Spectre Protection” button next to it. Good job we went offline, huh? InSpectre should now tell you that you're not protected in scary red letters.
Restart your system, making sure you're still offline, and wait for any startup programs to get up and running. Now it's time to run your benchmark. We're taking three 1080p encoding runs in x264 to work out an average, just for a little more accuracy down the line.
With those three numbers gathered and logged, we'll grab another useful bit of data by unRAR-ing the x264 install folder onto our desktop three times, and noting down how long it takes each time. This gives us an insight into disk access, as well as raw CPU grunt in a synthetic benchmark.
It's finally time to wrap ourselves back up in the warm blanket of Meltdown and Spectre protection, so go ahead and open InSpectre, and enable the two options on the lower part of the window. Reassuring green writing should now tell you that you're safe again. Phew!
Give your PC a restart and once again allow all startup programs to get back up to speed. Finally, run x264 or your chosen benchmark three more times, then unRAR the installer folder on to your desktop three more times, and gather the data. When you're finished, don't forget to re-enable your Internet connection.
Observe the difference, weep into hands
The differences in your numbers will vary from system to system. Probably, they represent a 3–15 percent decrease in performance with Meltdown and Spectre protection enabled, with your decompressing numbers falling toward the higher end, and CPU benchmark performance varying more marginally. If you're seeing differentials much bigger than that, there's almost certainly another factor at play, so don't go cursing those fixes just yet. Simply run more tests, ensuring other variables aren't messing with your figures.
Is a 3–15 percent performance hit acceptable? Considering the dire consequences of someone using the Meltdown or Spectre exploits to access your passwords and other personal info from your kernels, we think it is. No shrinkage in system grunt is to be welcomed with open arms, but thankfully it looks like the impact of these fixes is unlikely to prove noticeable in everyday usage.
Boiling point
How did these two notorious CPU exploits come to be in the first place? And why did it take their manufacturers over 20 years to realize their architectures were at risk? The answers to those very pressing questions still haven't been provided, and perhaps even more chilling is the fact that they were discovered by complete accident by three different research teams, working independently, at almost exactly the same time.
That the exploits affect CPUs dating back to 1995 but weren't spotted and shown to Intel until June 2017 suggests that many previous researchers were aware of it, but didn't act upon it. It's more comforting to imagine that it was blind coincidence, though, so let's ensconce ourselves in that theory.
Prior to their discovery, it was long held true that virtual memory data held in the CPU cache was as good as under lock and key. Processes simply couldn't access that data without the proper authorization—so everyone erroneously thought. Both Meltdown and Spectre work in a broadly similar way, accessing the CPU cache and all the riches it contains. And because the problem is fundamental to CPU architectures that have been iterated on for over 25 years, nearly every Intel and AMD processor produced during that period is affected.
This article was originally published in Maximum PC's June issue. For more quality articles about all things PC hardware, you can subscribe to Maximum PC now.
Phil 'the face' Iwaniuk used to work in magazines. Now he wanders the earth, stopping passers-by to tell them about PC games he remembers from 1998 until their polite smiles turn cold. He also makes ads. Veteran hardware smasher and game botherer of PC Format, Official PlayStation Magazine, PCGamesN, Guardian, Eurogamer, IGN, VG247, and What Gramophone? He won an award once, but he doesn't like to go on about it.
You can get rid of 'the face' bit if you like.
No -Ed.

 Join The Club
Join The Club